
- Why Regular Data Recovery Tools Can’t Restore Files from RAID
- Key Information About the NAS Infortrend EonStor GSe Pro 1004
- How to Remove Hard Disks from Your NAS and Connect Them to a PC
Why Regular Data Recovery Tools Can’t Restore Files from RAID
Conventional hard drives store user data by writing it sequentially across the disk surface, which means an entire file is typically located on a single drive. In contrast, when data is written to a RAID array, each file is split into multiple fragments. These fragments are then distributed and written in sequence across all the drives in the array. Depending on the configuration, fragment sizes can range from 2 KB to 2 MB, so every file is physically stored across several disks at once.
This approach significantly increases read and write performance — after all, writing two halves of a 1 GB file to two drives simultaneously is much faster than writing the full 1 GB to a single disk. However, this same mechanism makes file recovery far more complex.
Different RAID levels use different methods to distribute and protect data. On top of that, manufacturers like Infortrend often add their own proprietary structures and variations. As a result, data can be written to disks in many different formats, and each requires a specific approach during recovery.
What are the common causes of data loss in NAS Infortrend EonStor GSe Pro 1004 devices?
There are several common causes of data loss in NAS Infortrend EonStor GSe Pro 1004 devices, including:
- Hardware failure: This can include issues with the hard drives, power supply, or other components of the device. If any of these components fail, it can result in data loss.
- Accidental deletion: Users may accidentally delete important files or folders, leading to data loss. This can happen due to human error or improper file management practices.
- Software corruption: Corruption of the NAS operating system or other software can result in data loss. This can occur due to malware or viruses, improper shutdowns, or software bugs.
- Power outages: Sudden power outages or fluctuations can cause data loss if the device is not properly protected with backup power or surge protectors. Power loss during read or write operations can result in data corruption or loss.
- Natural disasters: Events such as floods, fires, earthquakes, or other natural disasters can physically damage the NAS device and result in data loss.
- Theft or physical damage: If the NAS device is stolen or physically damaged, data loss can occur. It is important to have proper security measures in place to protect the device from theft or damage.
- User error: Users may unintentionally modify or delete important files or folders, leading to data loss. This can happen due to lack of knowledge or training on how to use the NAS device properly.
To minimize the risk of data loss, it is recommended to regularly backup data from the NAS device to an external storage or cloud storage solution. Additionally, implementing proper security measures, such as firewalls and antivirus software, can help protect against malware and viruses.
How to Remove Hard Disks from Your NAS and Connect Them to a PC
Although the NAS EonStor GSe Pro 1004 can be accessed over the network, you still need to remove its hard disks and connect them directly to a Windows PC. Only then can the recovery software properly scan and analyze the drives. Follow these steps:
-
Power off the NAS and disconnect it from the power source.
WARNING! Before removing any drives, carefully read the device manual. Improper actions may damage both the NAS enclosure and the hard disks in the RAID array.
-
Remove the hard disks one by one, gently sliding each drive out of its slot. Remember that hard disks are highly sensitive: any impact or drop can cause serious physical damage.
-
Label each hard disk according to its position inside the NAS. The order of the drives is crucial for correct RAID reconstruction.
-
Connect the drives to your computer. In this video, we explain which ports you can use to connect hard disks and what to do if your PC does not have enough free connectors.
Go to view
Step-by-Step Data Recovery with Hetman RAID Recovery
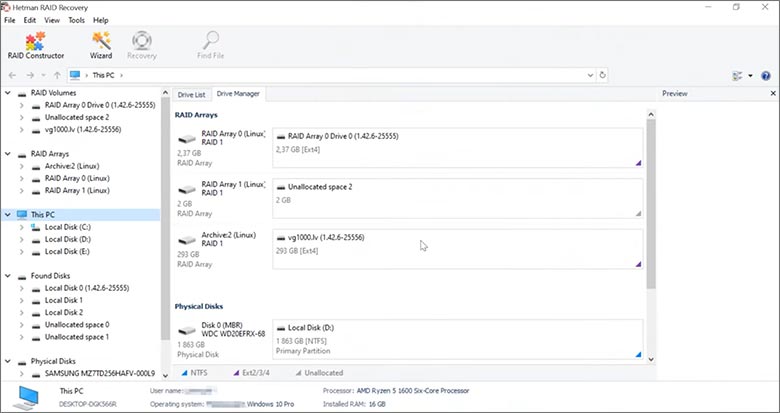
This program restores data from damaged RAID arrays and is fully compatible with Infortrend EonStor GSe Pro 1004. Each hard disk in the array contains technical metadata describing how files were written. When launched, Hetman RAID Recovery analyzes this metadata, automatically reconstructs the damaged array, and provides access to its contents. After that, you can browse the recovered disk and save your files. The program can also restore files that were accidentally deleted from the network drive.
How to recover data from a Infortrend
EonStor GSe Pro 1004 has 4 HDD slots, and it supports the following array types:
- RAID 0;
- RAID 1;
- RAID 5;
- RAID 6;
- JBOD;
NAS supports:
- exFAT, VFAT, FAT 12 / 16 / 32;
- NTFS / ReFS;
- APFS / HFS+;
- Ext2 / 3 / 4 / ReiserFS / XFS / UFS / ZFS / Btrfs;
- VMFS / HikvisionFS;
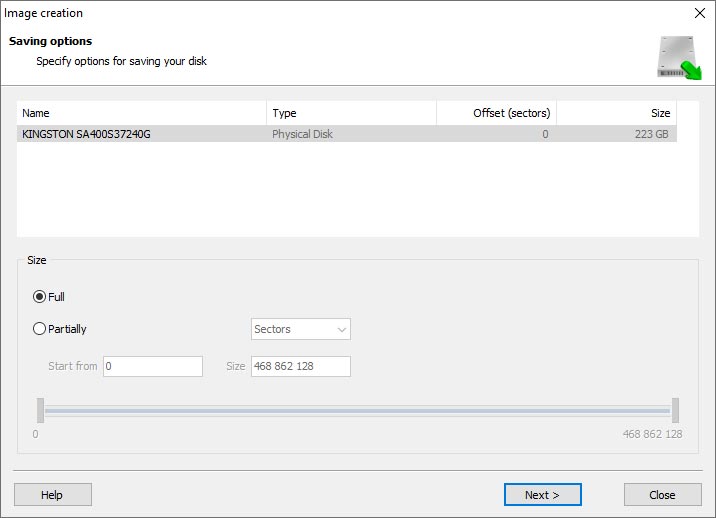
How to Safely Recover Data from Disk Images
This utility allows you to create a complete copy of a disk and work with the disk image instead of the physical drive. This approach helps protect your data from:
- Overwriting during the recovery process;
- Additional data loss caused by bad sectors;
- User errors.
To create a disk image, follow these steps:
-
Ensure you have enough free space to store the image. Its size will typically match the size of the original disk.
-
In the main window, select the target disk and choose Tools - Save Disk. You can also select multiple disks if needed.
-
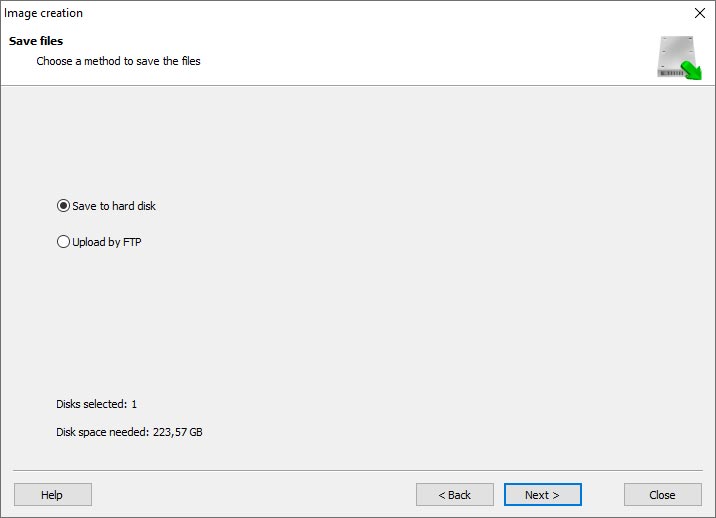
When the Image Creation Wizard opens, select whether you want to save the entire disk or only a specific region. Adjust the settings and click Next.
-
Choose the directory where the image will be saved. You may select any available disk connected to your PC or upload the image via FTP.
Where Are the User’s Files Actually Stored?
The Infortrend EonStor GSe Pro 1004 network-attached storage keeps OS Linux operating system files on a separate RAID 1 (mirrored) array. Usually, all NAS systems create several volumes on every hard disk, and the first of them takes up to 2 Gb of space. This is where operating system files are stored. Other volumes are united into a RAID array where user’s data is written.
RAID Recovery Software: Detailed Comparison
| Product | Operating system | RAID controller support | Supported file systems | Virtual RAID controller support | Data recovery from damaged RAID | File preview |
|---|---|---|---|---|---|---|
| Hetman RAID Recovery | Windows, Linux, MacOS | Yes, over 100 controllers | FAT, exFAT, NTFS, ReFS, APFS, HFS+, Ext4, Ext3, Ext2, ReiserFS, Btrfs, VMFS, Hikvision, XFS, UFS, ZFS | Yes | Yes | Yes |
| DiskInternals RAID Recovery | Windows | Yes, over 10 controllers | FAT, NTFS, Ext2/3/4, HFS+ | No | Yes | Yes |
| R-Studio | Windows, Mac, Linux | Yes, over 20 controllers | FAT, NTFS, Ext2/3/4, HFS+ | Yes | Yes | Yes |
| UFS Explorer RAID Recovery | Windows, Mac, Linux | Yes, over 100 controllers | FAT, NTFS, Ext2/3/4, HFS+ | Yes | Yes | Yes |
| EaseUS Data Recovery | Windows | Yes, over 20 controllers | FAT, NTFS, Ext2/3/4, HFS+ | No | Yes | Yes |
| ReclaiMe Free RAID Recovery | Windows | Yes, over 100 controllers | FAT, NTFS, Ext2/3/4, HFS+ | Yes | Yes | Yes |




Data recovery from a NAS device can still be possible even if the device is showing signs of overheating or cooling fan failure. However, it is important to address the overheating issue or fan failure first to prevent further damage to the device and potential data loss.
Here are a few steps you can take:
Remember, it is important to prioritize addressing the overheating or fan failure issue before attempting any data recovery to minimize the risk of further damage to the device and potential data loss.